THORChain’s suspected multichain exploit and emergency halt on May 15 has turned into another DeFi security incident, and another test of cross-chain trust.
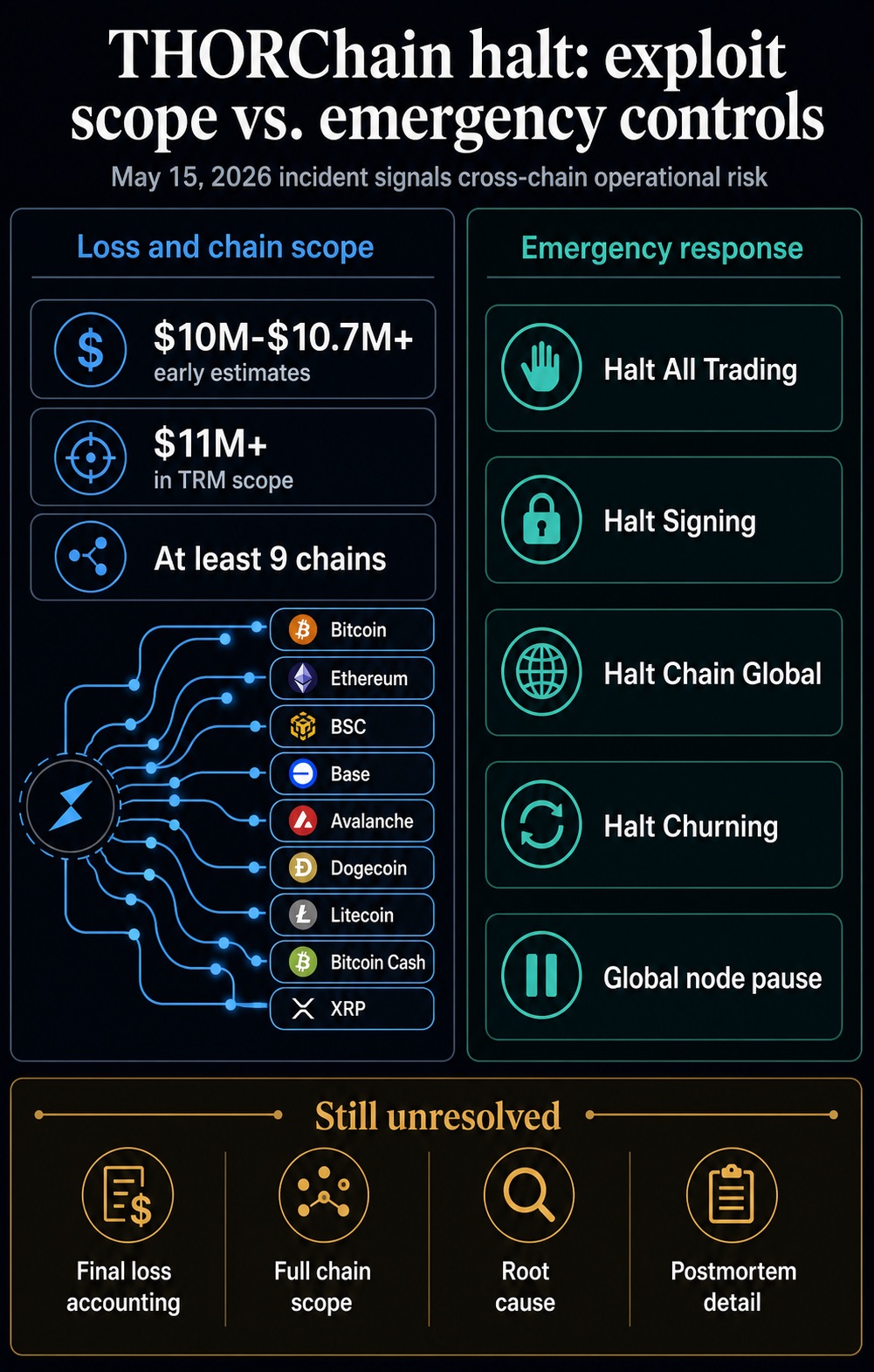
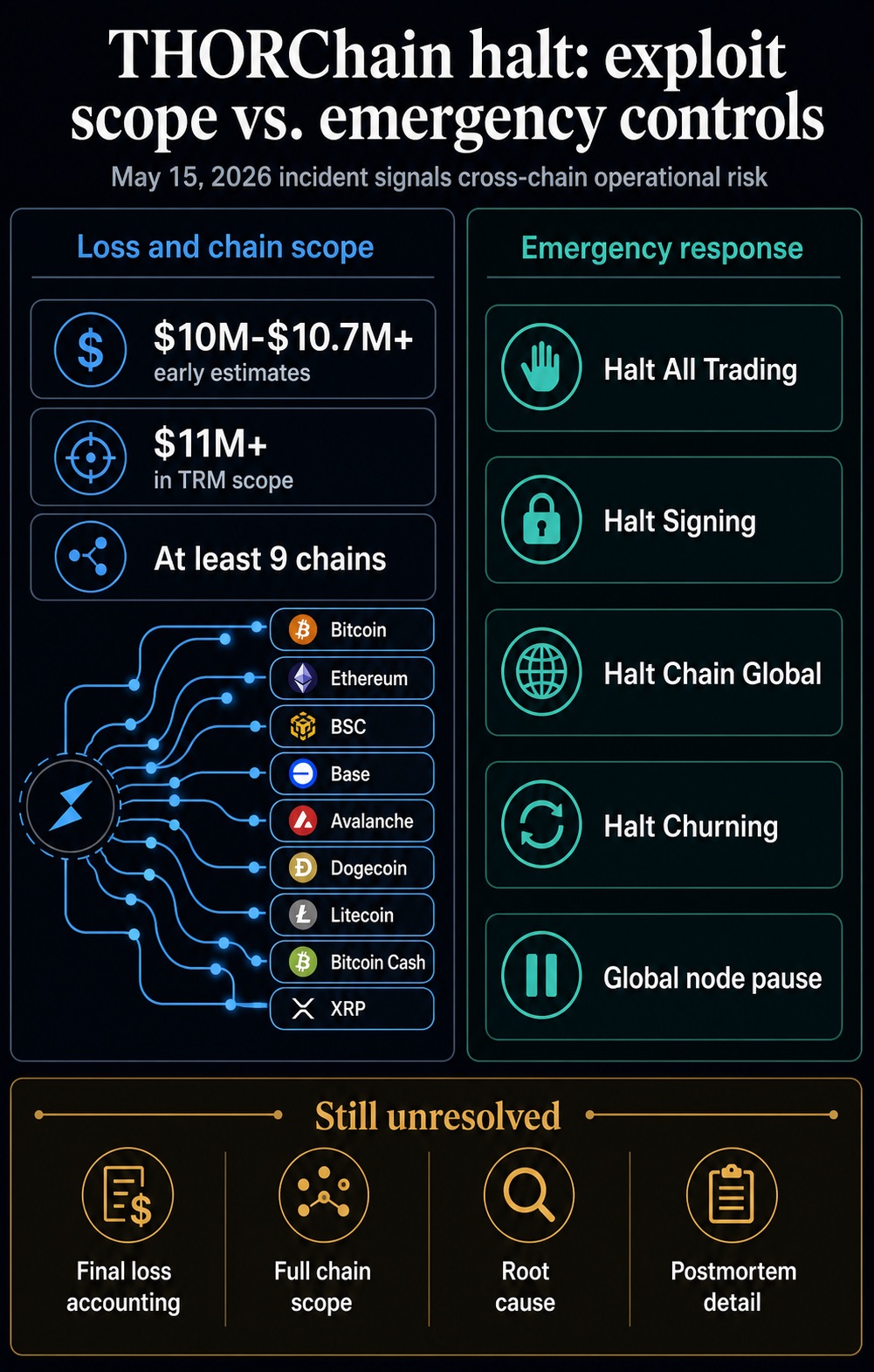
Emergency controls moved through chain-specific halts, Halt All Trading, Halt Signing, Halt Chain Global, Halt Churning, and repeated global node-pause updates.
One public alert described the likely exploit affecting Bitcoin, Ethereum, BSC, and Base, resulting in more than $10.7 million in losses, revised from an earlier $7.4 million estimate.
Another security estimate put the loss near $10 million, including 36.75 BTC and about $7 million across BNB Chain, Ethereum, and Base.
The chain scope was later expanded in a TRM Labs assessment, which reported that the attacker drained more than $11 million across at least nine chains. Those chains included Avalanche, Dogecoin, Litecoin, Bitcoin Cash, and XRP, in addition to the initial four-chain framing. The figures may still move as the accounting is reconciled, but the available record points to a multichain infrastructure event touching several native-asset routes.
The halt, therefore, carried consequences beyond THORChain. Cross-chain liquidity is supposed to make crypto feel more useful, liquid, and connected. Yet the same design that lets assets move between isolated networks can also compress the response window when something breaks.
In this case, DeFi’s promise of seamless routing ran straight into the need for an emergency stop.
The Halt Became The Signal
The operational response is documented in the chain’s emergency framework. THORChain’s procedures describe network and chain halts as tools node operators can use when funds are at risk.
Its architecture relies on Bifrost observation, vaults, and threshold-signature signing to move native assets across chains without wrapping them.
Those controls can protect funds by stopping further activity. They also show that cross-chain infrastructure is a stack of observers, validators, vaults, signing logic, node operations, and emergency procedures.
When that stack is tested, the market asks whether a single bug can be patched and whether the system can remain credible while the response itself disrupts routing.
I think that distinction brings the THORChain incident into the broader DeFi story. Mature financial infrastructure is expected to fail safely, explain quickly, and restore confidence with a documented root cause.
DeFi often moves faster than that standard. It ships integrations, new chains, and liquidity routes before users and institutions have a clear way to price the full operational risk.
A compact confidence ladder captures the current state of record:
| Signal | What is supported | What remains unresolved |
|---|---|---|
| Initial security alert | Likely exploit across Bitcoin, Ethereum, BSC, and Base for more than $10.7 million. | Final loss accounting and complete chain scope. |
| Independent estimate | About $10 million, including 36.75 BTC and roughly $7 million on EVM-linked chains. | Whether all affected assets and addresses have been fully reconciled. |
| Analytics scope | More than $11 million across at least nine chains. | How the wider scope maps to THORChain’s final postmortem. |
| Emergency controls | Trading, signing, global chain activity, and churning controls were activated. | How quickly the halt contained the damage and what activity resumed afterward. |
| Protocol confirmation | One of six Asgard vaults was reportedly compromised for roughly $10.7 million; initial indications said individual swaps were unaffected. | Final root cause, final user-impact accounting, and postmortem detail. |
The Trust Discount Is Now Measurable
The damage from exploits rarely ends with the drained wallet. Immunefi’s 2026 security findings put the average direct theft at $25 million, while the median loss fell to $2.2 million.
That gap shows a market where routine defenses may improve while the largest incidents still define confidence.
The same report found that the top five hacks in 2024 and 2025 accounted for 62% of stolen funds, and hacked tokens saw a median six-month decline of 61%.
Those token moves cannot be cleanly separated from market conditions or project-specific weakness in every case. Still, the pattern supports the core market reaction: exploits become long-tail business events.
They drain capital, consume team time, slow integrations, and make partners question whether the next failure will hit them indirectly.
The trust discount reflects an extra layer of skepticism toward a sector that wants to be treated as financial infrastructure, yet still produces failures that look like crisis drills.
Users, exchanges, market makers, custodians, and institutions require more evidence to trust a protocol’s uptime, monitoring, key management, and emergency processes.
Recent cross-chain incidents reinforce that point. In the KelpDAO bridge exploit, attackers targeted off-chain verification and source-chain watching infrastructure rather than a conventional smart-contract bug.
The result was a false view of reality that led to valid-looking transactions releasing funds. Bridge-security fears have already influenced infrastructure decisions, including Kraken’s move to use Chainlink CCIP for kBTC and future wrapped assets following the KelpDAO shock.
That makes the THORChain halt feel less isolated. The sector is being forced to prove that the trust path across chains is observable, redundant, and controllable before billions of dollars of liquidity are routed through it.
For institutional users, the issue becomes operational due diligence. Cross-chain exposure touches custody policy, liquidity commitments, incident response, and counterparty reviews.
A protocol that routes native assets across chains has to prove that the monitoring and emergency process around that routing is as strong as the connectivity itself.
For builders, that changes what counts as progress. New routes and integrations can deepen liquidity, but they also create more surfaces for monitoring, key management, and incident response.
The next credibility gains will come from showing that controls scale with liquidity before a failure forces counterparties to revisit assumptions.
THORChain Carries A Compliance Layer Too
THORChain’s position is especially sensitive because the protocol combines an attack surface with a routing role in major illicit-flow episodes.
As of TRM’s report, the May 15 exploit had no public actor attribution. That caveat keeps the current incident separate from earlier laundering cases unless new evidence changes the record.
The same analysis described THORChain as a recurring rail for moving stolen funds, including flows tied to the Bybit and KelpDAO incidents.
That pressure was evident after Lazarus-linked Bybit funds moved through the protocol, when THORChain faced tensions between developers and validators.
Federal investigators attributed the February 2025 Bybit theft of about $1.5 billion in virtual assets to North Korea’s TraderTraitor activity.
The FBI also urged private-sector crypto entities, including DeFi services and bridges, to block transactions to or from addresses linked to laundering.
That history sharpens the current episode. A protocol can be useful because it makes native cross-chain swaps efficient. The same utility can make it attractive to attackers and difficult for compliance teams to ignore.
Once a protocol is seen as both exploitable infrastructure and a route for illicit funds, counterparties have to price in more than just smart-contract risk.
They have to price operational interruption, screening exposure, and the chance that integrations become reputational liabilities.
RUNE price reaction stays secondary. Market data on May 16 put RUNE at around $0.44, down 21.90% over 24 hours.
The broader crypto market stood near $2.61 trillion with Bitcoin dominance at 60.2%. The market noticed the incident, but the more important question is whether liquidity providers, routing interfaces, wallet integrations, and compliance desks change behavior after the halt.
The important market signal will come from the next set of operational choices rather than from a one-day chart. Liquidity interfaces can route around protocols that introduce uncertainty; custodians and market makers can raise internal risk scores.
Compliance teams can demand better screening and incident records before supporting integrations. Those reactions are slower than a token selloff, but they are the way a security event becomes a durable trust discount.
That is the slower repricing institutions notice. It shows up in due diligence questions, integration queues, and risk limits long after the emergency halt leaves the alert feed.
The Next Test Is The Postmortem
The next test starts with more than a recovery message: THORChain needs to produce a clear postmortem, reconcile the final loss figure and chain count, explain the root cause without speculation, and show what changed in its vault, key-management, node, monitoring, and halt processes.
Recovery details may help contain user harm while leaving the infrastructure question intact.
If THORChain completes compensation, resumes safely, and documents a credible fix, the incident can remain a severe but contained confidence hit.
If the root cause remains unsettled, final accounting keeps changing, or integrations pull back, the event becomes another data point in a broader repricing of cross-chain DeFi.
That is the sector-level consequence. DeFi wants to present itself as a durable, always-on financial infrastructure.
Every major cross-chain exploit makes that claim harder to defend until the industry can show that the bridges, vaults, signing systems, and emergency controls connecting its markets are as mature as the capital they aim to attract.